25 September 2022
TL/DR
- Use an authenticator app like Google or Microsoft Authenticator.
- SMS and Email authentication are better than nothing but can be compromised.
- Turn off your bank app notifications.
- Never approve an authorization request that you have not initiated.
With the recent Optus hacks, it’s important for Australian consumers and brands to remain vigilant against identity theft and the associated financial consequences. With over 11.2 million Optus customers possibly impacted, hackers claim to have stolen names, dates of birth, phone numbers, email addresses, and, for a subset of customers, addresses and ID document numbers such as driver’s licenses or passport numbers.
Optus has started to communicate with their customers where individuals’ data has been flagged as being impacted by the breach. They are recommending ‘heightened awareness’ and that impacted customers activate Multi-Factor Authentication (MFA) on all of their accounts, among other security measures such as strong passwords, to prevent being compromised. So this blog looks at how effective is MFA in protecting customers’ data?
There is no doubt that MFA is the first line of defence against being hacked, but it is not foolproof and hackers have discovered workarounds where weaker versions of MFA such as email or SMS.
What is MFA?
Also known as Two-Step Verification, Multifactor Authentication requires at least two layers of authentication to prove who you are – beyond just a basic username and password entry. To login into a device or application, you will need a second thing – what we call a second “factor” – to prove who you are. This could be biometrics / fingerprint, an authenticator app code, email or SMS code verification etc.
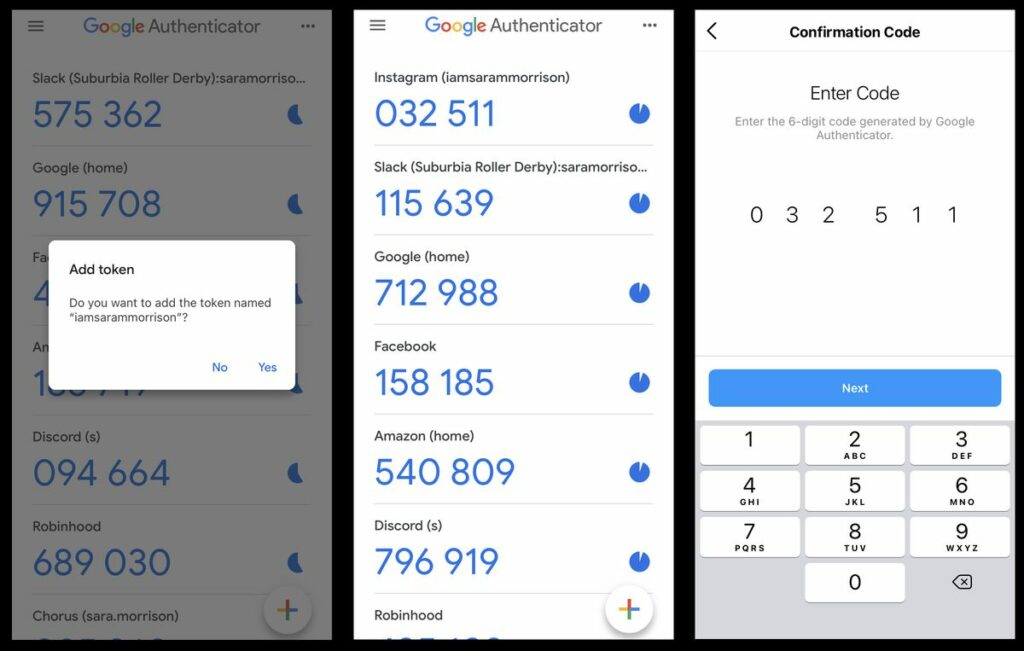
Example of Google Authenticator (not real codes)
There is no doubt that MFA is the first line of defence against being hacked, but it is not foolproof and hackers have discovered workarounds for weaker versions of MFA such as email or SMS.
SMS MFA can be compromised
Using SMS as a means to authenticate your password is better than nothing, but it’s not the most secure method. Putting aside the outages that often make SMS MFA unusable, SMS is not encrypted, meaning that it can be intercepted by criminals.
A more common scam that gets around SMS based MFA is called a SIM Swap – where criminals contact your existing provider and requests to activate a new SIM card with your number. If proper checks are not conducted by the carrier, or the criminal uses stolen data to authenticate your identity, they can take control of your phone number and send all messages to a device in their control, including your MFA codes.
A similar scam is called Unauthorised Mobile Porting. Porting is a legitimate service that allows customers to transfer a mobile number from one telecommunication provider to another. An Unauthorised Port occurs when a criminal contacts a different telephone provider, sets up an account with them and requests to have your number brought over from your current provider.
In both cases, Once a mobile number has been successfully taken over, criminals will receive your MFA text messages, including those containing password resets. This then gives them access to your existing online accounts, banking services etc.
This is not possible with Apps such as Google or Microsoft Authenticator because they store their secret keys in phone’s protected memory areas. If your phone isn’t rooted only your Authenticator app can get access to them. They cannot be intercepted or retrieved through sim swaps. So, your Authenticator apps are much more secure and reliable than SMS.
Always use an authenticator app like Google or Microsoft Authenticator over SMS!
A Reddit thread looked at the issue in light on the recent Optus hack and one user claimed that they went into an optus store this week to get new sim card and was not asked for any identity documents just the phone number of the account. If this is actually true, putting aside shockingly lax requirements to get a new SIM card, consumers should be extra vigilant and move to an authenticator app as soon as possible.
Another user u/leinad__m, claimed that only two days ago their partner’s phone number was ported to a new phone:
Email Authentication can also be compromised
Email authentication follows the same process as SMS MFA, but you receive a code to your email address instead of a text message. The problem with email as a MFA delivery channel is that if an attacker compromises your email account, they have your codes to potentially access other applications via password resets.
Turn Off your Bank App Notifications
A rash of thefts at UK gyms and health clubs is revealing a key flaw in how iPhone customers keep their bank accounts and money safe. The theft, in and around London, involved an individual stealing phones and bank cards from gym lockers. Once they have the phones and the cards, the thief registers the bank card on the relevant bank’s app using their own phone or computer. Since it is the first time that card will have been used on the new device, a one-off security passcode is demanded. That verification passcode is sent by the bank to the victim’s stolen phone, which then flashes up on its locked screen, allowing the thief to enter it into their own device. Once accepted, gets full control of the bank account. Experts are recommending that gym goers never leave their valuables in their locker, and consider disabling the “Show Notifications” option on their phones.
MFA Fatigue Attack: Hackers’ new tactic in major breaches
With the advent of multi-factor authentication, especially through employees’ smartphones, it was inevitable that a hack would be soon to follow. An MFA Fatigue attack is when a threat actor runs a script that attempts to log in with stolen credentials over and over, causing a repeated stream of MFA push requests to be sent to the account owner’s mobile device. The goal is to keep this up, to the point that the employee simply presses OK to clear the onslaught. If that does not work, the threat actors make contact through voice or email, imploring the user to accept the requests. This type of social engineering technique has proven to be very successful by the Lapsus$ and Yanluowang threat actors when breaching large and well-known organizations such as Microsoft, Cisco, and now Uber. The full story is available at Bleeping Computer.
About brandsec
brandsec is a corporate domain name management and brand security company that looks after many of Australia, New Zealand and Asia’s top publicly listed brands. We provide monitoring and enforcement services, DNS, SSL Management, domain name brokerage and dispute management and brand security services.