20 October 2022, by Ed Seaford
Avoiding Detection
Web monitoring tools play an important role in thwarting impersonation and phishing attacks, but cybercriminals deploy an array of evasion techniques to evade detection and carry out their nefarious activities. In my years assisting clients with the take-down of phishing domains, I’ve seen cybercriminals employ a myriad of evasive manoeuvres. They’re not just relying on sophistication; they’re capitalising on agility, speed and camouflage. In this blog, we delve into some of the common techniques that cyber-criminals use to fly under the radar. Armed with this knowledge, we hope that brand owners can adapt their defences and stay one step ahead.
Domain Fast Fluxing
This technique involves rapidly changing the IP addresses associated with a domain name. By frequently changing the location of phishing sites, cybercriminals make it harder for monitoring tools to keep up.
Fast fluxing ensures that even if one or more of the IP addresses hosting a phishing page are taken down or blacklisted, the domain can still resolve to other active IP addresses, keeping the phishing site operational.
Domain Fast Fluxing is akin to a shape-shifter constantly changing its form, making it difficult to target and neutralise. The best way to address Domain Fast Fluxing is to neutralise the domain name via a domain name suspension submission – this cuts the snake’s head off and means their revolving IPs are all useless.
Domain Generation Algorithms (DGAs)
DGAs create large numbers of domains in a short time. Only a few of these domains are activated, making it a challenge for defenders to predict which ones will be used.
DGA is a technique generally employed by malware wherein it autonomously produces numerous potential domain names to establish communication with its command and control (C&C) server. By dynamically generating a multitude of domain names, the malware ensures consistent communication channels, even if some domains are taken down or blacklisted. This approach not only impedes traditional domain-blocking methods but also complicates efforts by defenders to dismantle the malware’s C&C infrastructure, as the malware can shift to another generated domain if one becomes inaccessible.
it’s worth noting that the predictability of DGAs is also their Achilles’ heel. Once security personnel reverse-engineer a particular DGA, they can predict future domains the malware will attempt to contact. This allows for proactive defences, such as sinkholing the predicted domains, effectively disrupting the malware’s ability to communicate with its C&C servers.
Using Lesser-Known TLDs
Cybercriminals may register domains using lesser-known or newer top-level domains (TLDs), which might not be on the radar of some monitoring solutions.
Unlike the .AU domain name, certain TLDs may have less stringent registration and monitoring processes. This can allow bad actors to register malicious domains more easily and operate under the radar for longer periods.
Many cybersecurity tools and web filters might be initially configured to focus on more popular TLDs. As a result, a domain with a lesser-known TLD might not trigger alerts or be blocked by default.
Brands can use domain monitoring tools to watch for domain names similar to your brand’s, especially in lesser-known TLDs. Immediate alerts can help you act quickly.
Ephemeral Sites
Some phishing sites are only active for a short period, just long enough to snag victims. By the time they’re detected, they might already be taken down.
Many web monitoring tools scan the internet at intervals. By the time these tools identify and flag a malicious ephemeral site, it may have already been taken down by the attacker, thus evading longer-term detection.
Ephemeral sites, due to their transient nature, offer little time for investigators to trace back to the criminals. The short lifespan of ephemeral sites means they often disappear before any legal or technical takedown action can be executed.
To counteract the threat of ephemeral sites, organisations must employ real-time threat intelligence, heuristic-based detection, and proactive monitoring to detect and block these sites as quickly as they emerge.
Geofencing
Cybercriminals can configure their infrastructure to respond only to requests from specific geographic regions, making detection by monitoring tools in other regions difficult.
One of the primary reasons cybercriminals employ geofencing is to evade detection from security and monitoring tools. By restricting the access of their malicious content or infrastructure to specific geographic regions, they can make it significantly harder for global security teams to analyze or even see their threats.
Geofencing allows attackers to be precise about their target audience. If they’ve crafted a phishing campaign or other malicious activity tailored for a specific region, language, or cultural nuance, geofencing ensures only people from that region can access it.
Countering geofencing requires a mix of technology, strategy, and listening to your customers. Leveraging Virtual Private Networks (VPNs) allows them to mask geographic locations while establishing monitoring points in diverse regions ensure broad threat detection.
Content Delivery Networks (CDNs)
Attackers use CDNs to disguise their phishing sites’ locations, leveraging the CDN’s legitimacy to hide malicious content. While CDNs enhance web content delivery by distributing it globally, cybercriminals exploit this to obscure malicious content origins, making it harder for defenders to locate the threat. This CDN use can thwart typical blacklisting, as content appears from varied legitimate IPs.
To combat this, organisations should employ threat intelligence to spot unusual CDN activities, set domain-specific security rules, and deeply inspect web content. Behavior-driven detection, coupled with current threat insights, can address CDN-related risks.
Using Compromised Legitimate Websites
Instead of creating new malicious sites, cybercriminals sometimes compromise legitimate websites to host their phishing content.
This tactic exploits the site’s reputation, making users more likely to interact with malicious content, thinking it’s genuine, and thereby increasing the success rate of phishing, malware distribution, or data theft.
It also makes it more difficult to take down a legitimate website, because it often involves liaising with the Host, website owner and Registrar. Being able to distinguish a compromised website from a phishing site allows you to quickly implement a strategy that will quickly get the infringing content removed.
URL Shorteners and Redirection
Cybercriminals use URL shorteners and redirections to obfuscate the final destination of a malicious link, making it difficult for users and some security solutions to immediately recognise the threat.
These shortened or redirected URLs can disguise the malicious nature of a link, leading unsuspecting users to phishing sites, malicious downloads, or scam pages, all while hindering the ability of security tools to blacklist or detect the nefarious URLs.
To combat malicious URL shorteners and redirections, organisations should employ link-expansion tools and URL filtering. Additionally, training users to identify suspicious links minimises risks associated with deceptive redirects.
Web Content Cloaking
This involves delivering different content based on who is visiting the site. For example, a regular user might see a phishing page, while a security scanner might see harmless content.
Web content cloaking is a deceitful technique where attackers display different content based on the visitor’s profile, essentially “camouflaging” their malicious intent. A typical user might encounter a phishing page, while security scanners see benign content, allowing cybercriminals to evade detection and prolong their malicious campaigns.
To counter web content cloaking, organisations should regularly rotate user agents and IPs, and combine both automated scans and manual inspections. This multifaceted approach can unmask cloaked content, ensuring that malicious sites don’t slip through undetected.
Tor and Decentralised Networks
Cybercriminals use Tor and decentralised networks to cloak their activities and evade detection. The Tor network obscures a user’s location by routing traffic through multiple servers, while decentralised networks spread data across various nodes, preventing a single point of tracking. Such networks make it difficult to pinpoint and shut down malicious operations, offering attackers enhanced anonymity and resilience.
To counter the use of Tor and decentralised networks, organisations can block Tor exit node IP addresses, utilise advanced threat intelligence services to identify suspicious patterns and employ deep packet inspection to detect anomalous traffic.
Server Polymorphism
Server polymorphism involves changing the server’s content, structure, or behaviour dynamically to evade detection by security tools. In attacks, cybercriminals utilise server polymorphism to serve different payloads to different visitors or alter the behaviour of malicious servers when they detect scanning by security solutions.
By frequently modifying the appearance and behaviour of their malicious servers, attackers make it challenging for traditional signature-based security solutions to identify and block these threats. This tactic ensures the server remains operational and avoids detection for extended periods.
To combat server polymorphism, use behaviour-based detection and updated threat intelligence. Regularly patch systems to minimise vulnerabilities. Employ a multi-layered defence approach, including network monitoring, endpoint protection, and sandboxing, to detect and mitigate threats early.
Conclusion
Security professionals must continuously adapt and enhance their strategies, as cybercriminals keep innovating to bypass advanced security measures. By understanding these evasion techniques, security professionals can refine and enhance web monitoring tools to better detect and counteract phishing threats. However, it’s a continuous cat-and-mouse game as cybercriminals innovate in response to advancements in security measures.
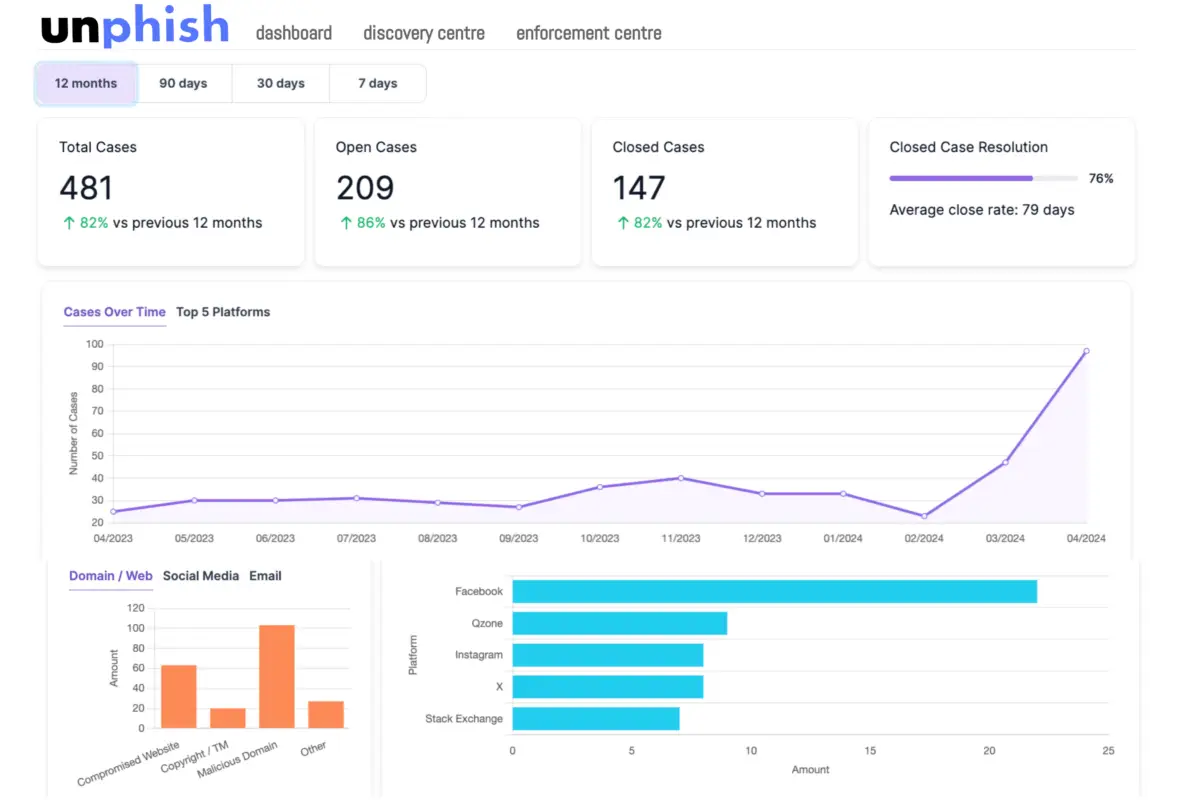
Remove Phishing Content Quickly and Effortlessly with Unphish
Sign up for early access to Unphish Beta and experience best in class takedown service
About brandsec
brandsec is a team of highly experienced domain name management and online brand protection experts. We provide corporate domain name management and brand enforcement services, helping brands eliminate phishing platforms across the internet. Supporting some of the largest brands in the region, we offer innovative solutions to combat threats across multiple industries.