Protection from Phishing Domains
As the prevalence of domain name-based phishing attacks continues to rise, it has become increasingly important for brands to take proactive measures to protect themselves. One of the most critical steps in this process is the identification and quick resolution of suspicious domain names that could be used by cybercriminals to impersonate the brand and engage in fraudulent activity.
According to the Australian Competition and Consumer Commission’s Scamwatch, Australians reported more than 74,000 phishing attacks with financial losses of more than $24.6 million last year. They estimate that only 13 percent of victims will lodge a report. In this blog, we look at proactive steps brands can take to protect themselves from domain name-based phishing attacks.
Defensive registrations
Domain-based phishing attacks are becoming harder to recognize, and bad actors are becoming more adept at tricking targets with misspellings and variations of a legitimate brand’s domain name. One common tactic used by phishers is to register domain names that are similar to the target brand’s domain name, with slight variations in spelling or extension. For example, a bad actor could target microsoft.com and replace the “m” with “n” to create nicrosoft.com to trick email recipients.

A phishing-based domain name using a misspelling of microsoft.com to trick customers into clicking on a suspicious link.[/caption]
To develop a typo-spelling defensive domain name registration strategy, consider how your domain name can be altered slightly to trick email recipients or website visitors. Common ways bad actors trick end users by altering the spelling of domain names include:
– Transposing two letters in a domain name, for example, micorsoft.com
– Incorrectly spelling a domain name to make it look like the real domain name, for example, nicrosoft.com
– Registering an identical version of your domain name in another domain name space, for example, microsoft.co or microsoft.com.ai-
– Punycode domains, where bad actors replace English letters with Greek or Acrylic letters, for example, Мicrosoft.com. In this eample, we have used the Greek M in place of the English “m.” These are very hard to detect.
Create a budget, so you don’t get carried away with defensive domain name registrations and focus on the most obvious domain name misspellings. Review annually – It’s important to review how bad actors are changing their registration tactics and make adjustments when new patterns or registration behaviours are detected.
Monitor for suspicious domain name registrations
Brands can monitor for newly registered domains that contain their brand name or similar variations. This can be done through automated tools or by conducting regular manual searches. If a suspicious domain is identified, brands can take immediate action to have it taken down.
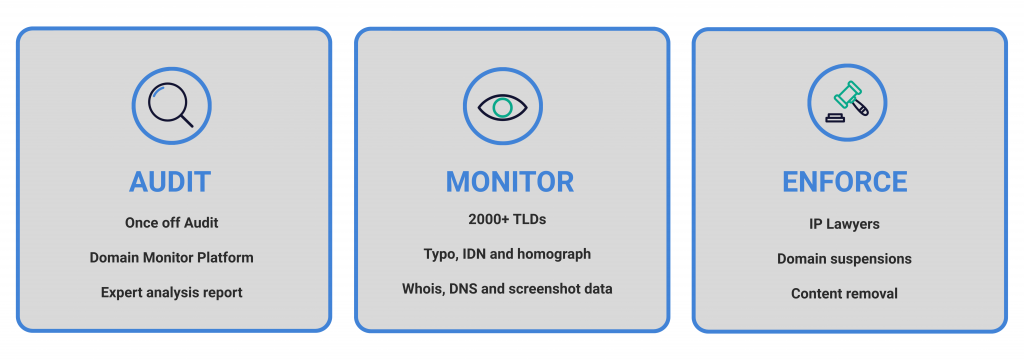
Our domain name monitoring tool is one of the most comprehensive in the world, covering thousands of domain name spaces and Registry DNS zone files. It identifies cybersquatting, typosquatting, potential phishing domain names, look-alike domains, punycode domains, homographic domains, scam domains, and competitor registrations.
Implement email authentication protocols
Spammers can forge (or spoof) your domain to send fraudulent messages that impersonate your organisation. Email authentication stops this by ensuring only authorised servers can send on your behalf.
DMARC (Domain-based Message Authentication, Reporting and Conformance) tells receiving mail servers what to do when they receive an email that claims to be from your domain but fails authentication. Messages that don’t pass may be fraudulent or sent from unauthorised sources.
DMARC works in combination with two key authentication methods:
- SPF (Sender Policy Framework): Allows a domain owner to specify which mail servers are authorised to send email for the domain. Receiving servers check if the message originates from an approved source.
- DKIM (DomainKeys Identified Mail): Adds a digital signature to every outgoing message. This ensures the message is authentic and has not been tampered with during transit.
Together, SPF, DKIM, and DMARC protect your organisation’s domain from spoofing, improve email deliverability, and help build trust with recipients.
Educate employees and customers
Educating employees and customers on how to recognise and report phishing attacks can be an effective way to prevent them. This can include providing training on how to identify suspicious emails or websites and encouraging customers to report any suspicious activity related to the brand.
Overall, a combination of proactive measures such as domain name registration, email authentication, monitoring, and education can help brands to protect themselves from domain name based phishing attacks.
As the prevalence of domain name based phishing attacks continues to rise, it has become increasingly important for brands to take proactive measures to protect themselves. One of the most critical steps in this process is the identification and quick resolution of suspicious domain names that could be used by cybercriminals to impersonate the brand and engage in fraudulent activity. In this regard, brands must remain vigilant and stay ahead of the curve by implementing robust measures that allow for the timely detection and elimination of potential threats.
About brandsec
brandsec is a team of highly experienced domain name management and online brand protection experts. We provide corporate domain name management and brand enforcement services, helping brands eliminate phishing platforms across the internet. Supporting some of the largest brands in the region, we offer innovative solutions to combat threats across multiple industries.