15 December 2022
DNS Attacks: DNS, or the Domain Name System, is a critical infrastructure technology that is used to translate human-readable domain names into the numerical IP addresses that computers use to communicate with each other on the internet. As with any network-facing technology, there are potential security threats that organizations using DNS should be aware of.
DNS DDoS Attack
A DNS DDoS attack is a type of cyberattack that uses a distributed denial-of-service (DDoS) attack to target a DNS server. In a DNS DDoS attack, the attacker will use a network of compromised computers, also known as a botnet, to send a large number of DNS queries to the DNS server. This can overwhelm the server and cause it to become unavailable, preventing legitimate users from accessing the internet or certain websites.
A common type of DNS DDoS attack is what is called a DNS Amplification Attack. In a DNS amplification attack, the attacker will send a large number of DNS queries with forged source addresses to open DNS resolvers on the internet. The open resolvers will then respond to the queries with large DNS responses, which are sent to the target’s IP address. Since the responses are much larger than the original queries, the attacker can amplify the traffic and overwhelm the target with a large amount of data.
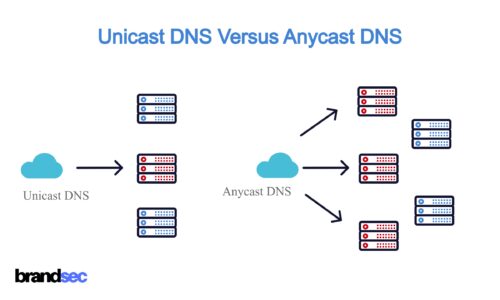
DNS DDoS attacks can be carried out in various ways, such as by using malware to compromise a large number of devices and turn them into part of the botnet, or by using a botnet-for-hire service to launch the attack. Large DNS networks can protect against DDoS attacks that use DNS load balancing to distribute queries across their extensive network and reduce the impact of the attack. You can also use services that specialize in mitigating DDoS attacks, such as cloud-based DDoS protection services.
DNS Spoofing Attack
In DNS spoofing, the attacker typically exploits vulnerabilities in the DNS server software or compromises the server itself in order to modify the DNS records. This allows the attacker to redirect users to a malicious website, even if they enter the correct URL for a legitimate website.
DNS Cache Poisoning Attack
In DNS cache poisoning, the attacker sends large numbers of DNS queries with forged source addresses to the DNS server, in an attempt to overload the server’s cache and insert malicious DNS records into it. This allows the attacker to redirect users to a malicious website even if they have not visited the website before, and the DNS records for the website are not yet in the server’s cache.
DNS man-in-the-middle Attack
A DNS man-in-the-middle (MITM) attack is a type of cyberattack where the attacker intercepts and alters DNS queries and responses. In a DNS MITM attack, the attacker can redirect users to a malicious website, even if they entered the correct URL for a legitimate website. This can be done by modifying the DNS records on a DNS server, or by intercepting and modifying DNS queries as they are sent over the network. To protect against DNS MITM attacks, you can use DNSSEC to authenticate DNS records and prevent tampering.
DNS Hijacking Attack
DNS hijacking, also known as DNS redirecting, is a type of cyberattack where an attacker modifies the DNS settings on a device or network to redirect traffic to a malicious website. In DNS hijacking, the attacker will typically change the DNS settings on a device to point to a malicious DNS server controlled by the attacker. This allows the attacker to redirect the victim’s internet traffic to a different website, even if the victim enters the correct URL for the legitimate website.
DNS hijacking can be carried out in various ways, such as by compromising the device or network, or by using malware to modify the DNS settings on the victim’s device. To protect against DNS hijacking, you can regularly check your DNS settings and make sure they are correct, and use secure DNS resolvers that support DNSSEC to authenticate DNS records and prevent tampering.
Tips for Preventing DNS Attacks
To prevent DNS attacks, you can use the following tips:
- Use DNSSEC to authenticate DNS records and prevent tampering.
- Use secure DNS resolvers that support DNSSEC, such as UltraDNS
- Regularly check your DNS settings and make sure they are correct.
- Use DNS load balancing and DNS caching to distribute the load among multiple DNS servers and reduce the impact of attacks. This is inherently built into Enterprise DNS services like UltraDNS.
- Use services that specialize in mitigating DDoS attacks, such as cloud-based DDoS protection services, such as UltraDNS Protect.
- Keep your devices and network secure by using strong passwords, regularly applying security updates, and using antivirus and anti-malware software.
By following these tips, you can help to protect your DNS server and network from attacks. The biggest thing that you can do to protect your business from these types of attacks is to engage an enterprise-grade DNS solution that has the technology, security, and scale and prevent these types of attacks. To discuss further please contact brandsec for a DNS consultation.
About brandsec
Brandsec is a corporate domain name management and brand protection company that look after many of Australia, New Zealand and Asia’s top publicly listed brands. We provide monitoring and enforcement services, DNS, SSL Management, domain name brokerage and dispute management and brand security consultation services.